Table of contents
Open Table of contents
Intro
In 2020, I was just beginning my journey into professional IT and cybersecurity. Today, I’m fortunate to work as a senior detection engineer at a leading MDR provider, with firsthand experience in a wide range of threat detection, investigation, and response scenarios. Along the way, I’ve picked up a variety of technical skills and an alphabet soup of certifications — many of which I never expected to be within reach when I was starting out.
What happened? How did I get here? The short answer: I spent a lot of time learning and thinking carefully about what I should learn and how I should learn it.
In this blog post, I’ll go over what I feel are the most important aspects of early professional development in a career in IT and/or Cybersecurity. I’ll also go over several common “early career” questions such as whether to attend college and if one should work on the blue team (a defensive role) or on the red team (an offensive role).
 Snake from Metal Gear climbs the IT security career ladder
Snake from Metal Gear climbs the IT security career ladder
What Do I Want to Do?
The first question you need to ask yourself in your career journey is “What do I want to do?” This question drives the beginning, middle, and end of your adventure, and can be based on many factors.
“What do I want to do?” (or “What do I want to be when I grow up?”) can seem lofty and difficult to answer. The solution to this conundrum can depend on things like salary expectations, work/life balance considerations, and day-to-day job details. Early on, I recommend picking a broad direction and marching in it. There are plenty of opportunities to specialize or pivot elsewhere as you progress in your journey. I initially came to the conclusion that I wanted to be a network engineer.
The rough series of questions I answered for myself when I was in high school are as follows:
- What do I not want to do?
- I didn’t want to do blue-collar work. I didn’t think I would be very good at physically exhausting work. This led me to conclude that I wanted to work in an office environment, given that nearly every major business has at least one corporate office.
- Given my constraints, what general options are available to me?
- There are many jobs in an office environment. Human resources, marketing, accounting, IT, and legal are all common dedicated functions in any organization.
- What general option available to me fits me best?
- Since I spent more time on my computer than most things in my life, I figured IT might be a good fit.
- What is a role (job title) in that job category that I can see myself working in, has jobs available, and can meet my salary expectations?
- A good starting place to answer this question is at the Bureau of Labor Statistics’ website. See their page for “Computer and Information Technology Occupations.”
- From my own personal knowledge, I knew the job title of “network engineer” (or “network guy”) existed and that it had jobs available (every company needs a network guy to make the Internet work, right?) A quick search using Google, Indeed, or Monster revealed that postings that disclosed salaries met my expectations for a livable wage in my area.
Using a similar line of questioning, I may have similarly concluded that I wanted to be a system administrator, an IT service desk analyst, a database administrator, and more. Early in a career, I do recommend focusing on jobs that do appear to have early career or entry-level opportunities. Unfortunately, although cybersecurity has a “shortage” of workers, most of the “cool” roles (incident response, digital forensics, penetration testing, red teaming) lack workers in the upper levels, not the entry level. Starting in a less crowded entry-level role early in your career (e.g., help desk analyst, network field technician) can be a great way to secure a position and develop the technical skills needed to stand out and pivot into a “cooler” cybersecurity role later.
I’ve included discussions on choosing to work in defensive security (“blue team”) or offensive security (“red team”) as well as whether to work in the private or the public sector in the appendix, linked below:
What Should I Learn?
Picking “what” to learn is perhaps the most important decision you can make while navigating the road of professional development. It’s a high-stakes item. Learning things can take a lot of time, one of your rarest and most precious resources. What you learn determines what hard skills you possess or are most easily able to develop. Ultimately, any IT or cybersecurity role is going to require some hard skills. Regardless of how likable and great a team player someone may be (extremely important things!), if they don’t understand IP addressing, they probably wouldn’t make a great network administrator.
Certification Roadmaps to Understand Required Skills
While you might have a rough idea of what you should learn (e.g., “networking”), you might not have a great understanding of where to start. Should you go learn Juniper switch CLI commands? Maybe, but that definitely shouldn’t be the first thing you learn in computer networking.
Many certification bodies offer roadmaps to guide you along your skill development process. The idea behind these roadmaps is to outline a progression from junior to senior roles with a “path” of skills and certifications to acquire at each stage of your career.
This roadmap from CompTIA, for example, orders certifications from beginner to expert for different job roles. Don’t worry, you don’t need to treat a roadmap like this as a bingo card or checklist — you can have a completely successful career with no or very few certifications at all!
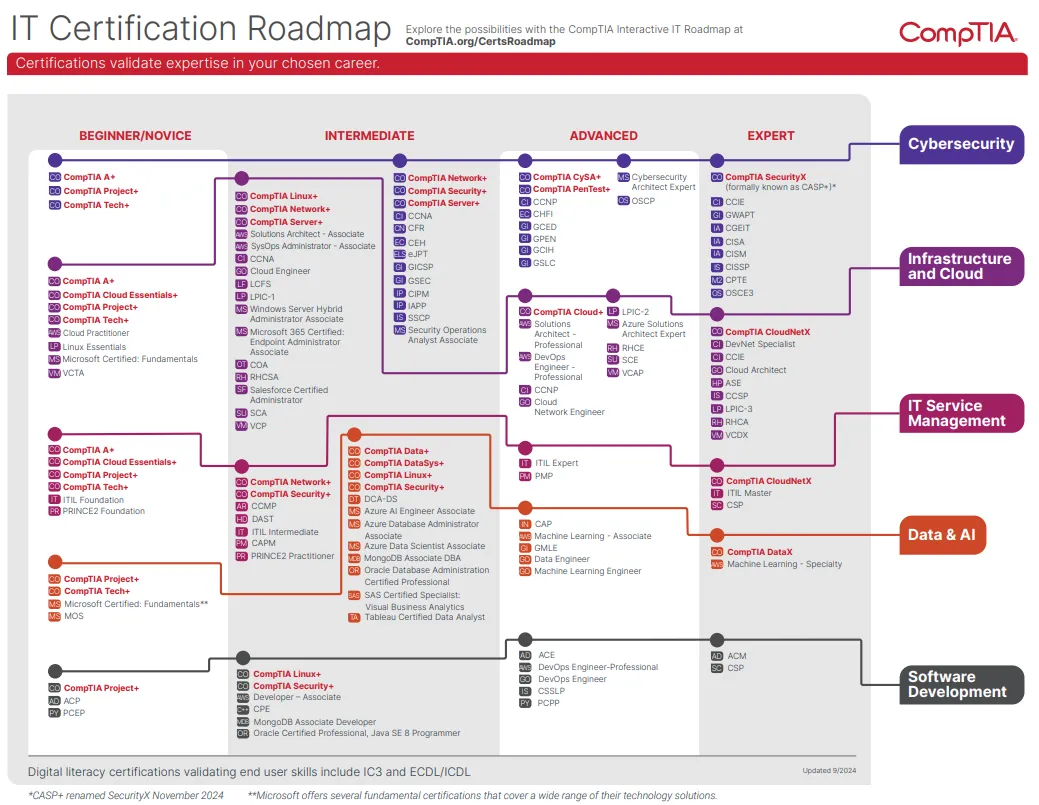
While not bad, I think this (and any roadmap coming from a specific certification vendor) leaves some things to be desired. The first issue is that vendors typically highlight their own certifications before any others. Second, the “roles” described here are not as accurate or nuanced as they could be. For example, “cybersecurity” being its own role in the roadmap is silly, as the field is too broad to be lumped into just one category.
My favorite is Paul Jerimy’s Security Certification Roadmap. Paul’s website does a pretty good job of enumerating relevant industry certifications as well granularly breaking down job roles.
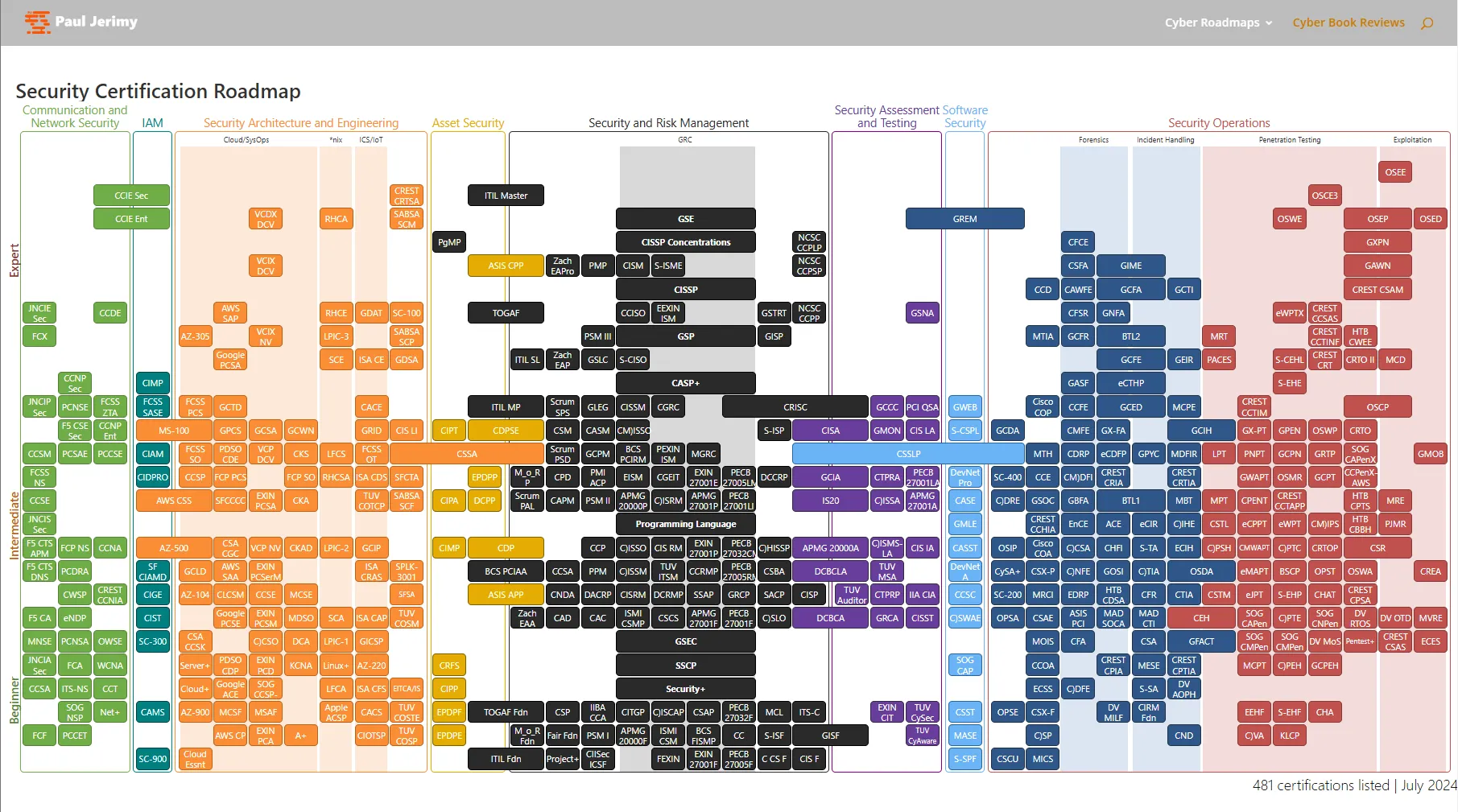
Even if you have no intention of ever becoming certified in anything, roadmaps like this can provide significant value.
Certifications Without Getting Certified
I like certifications. I think becoming certified in a discipline provides an opportunity for one to reinforce and affirm their knowledge and skills. However, I am also keenly aware that certifications cost money. And getting certified can take quite a long time, especially if you intend to get a good score on an exam. That is why I’m very happy to report that certifications provide great value, even if you don’t seek to acquire any.
For most certifications from most vendors, a publicly accessible objectives list exists. Simply Googling “CompTIA Network+ Objectives” yields multiple PDF results that enumerate all of the objectives of the CompTIA Network+ certification exam. For example, under “1.0 Networking Concepts,” CompTIA advises that you should understand routers, switches, firewalls, load balancers, intrusion detection systems, and proxies.
To put it another way, these objectives are basically a list of everything that you should know to be a junior network engineer. And because certifications require relevancy to the market to have value, this list is often significantly more accurate than most other sources, including, at times, university curricula. Not sure where to start when learning networking? Refer to the Network+ exam objectives! Not sure what to learn after that? Check out the CCNA exam objectives! And so on.
But What Should I Specifically Learn?
Once you’ve picked a general topic you want to learn — like firewalls — you may realize that the topic is not granular enough to “go learn.” Which firewall? Windows firewall? Linux firewall? And if you choose a Linux firewall, should you learn UFW, Firewalld, iptables, or all of them? But what about dedicated firewall appliances like pfSense and FortiGate devices? Should you start there?
Shortly after I first started in a SOC role, someone suggested to me that I should spend a lot of time learning iptables, the utility to manage IP packet filter rules in the Linux kernel. This wasn’t great advice. Not because iptables is bad or that I would never need to configure iptables in my life, but because it didn’t have relevance in any role I anticipated I would be interested in. Even if I wanted to pursue becoming a network engineer, better uses of my learning time included:
- Next-Generation Firewalls (NGFWs) from Palo Alto Networks, Fortinet, Check Point, or Cisco
- Network switches from Cisco, Arista Networks, or Juniper Networks
- SD-WAN technologies from Fortinet, Cisco, or VMware
Why would these have been better uses of my time? Because they are common in modern network engineering jobs. How do I know this? Because analyst firms (specifically, FIGs) tell me so.
Using FIGs Reports to Guide Skill Growth
The acronym “FIG” stands for Forrester, IDC, and Gartner. These are the biggest players in the “research and advisory” or “analyst firm” space. The only thing you need to know about these companies is that they are trusted by large organizations and the Fortune 500 for their opinions on what products to use. If something is in the upper-right of the IDC MarketScape report, the Forrester Wave, or the Gartner Magic Quadrant, big companies use it.
If I had the goal of becoming a security operations center (SOC) analyst, I would first learn what hard skills are required for the role. I would discover that using or understanding endpoint detection & response (EDR) technology is very important in a modern SOC. A quick Google Images search of "edr gartner magic quadrant" "2024" is going to yield a picture from a SentinelOne blog post highlighting their position in the magic quadrant. While I won’t repost that publicly available image (as I do not have prior approval to do so), you’ll see names like CrowdStrike, Microsoft, SentinelOne, and Palo Alto Networks in the top-right corner. From firsthand experience, I will tell you that these vendors are deeply relevant to modern SOC analysts.
Where do I Learn?
Once you’ve identified what you want to do and what you want to learn, you need to figure out where you want to learn from. This is another spot where you can end up wasting a lot of time if you make a poor decision. I’ve compiled a list of common IT and cybersecurity learning sources that I have personal experience with and their pros/cons down below:
| Learning Source | Pros | Cons | Comments |
|---|---|---|---|
| SANS | SANS provides the time-effective and highest-quality training that exists, period. SANS/GIAC certifications are some of the most well-recognized and highly sought-after. | SANS training and the corresponding GIAC certifications are expensive. | I’d recommend taking at least one in-person SANS class and going through the process of getting GIAC certified in your life. It’s a great experience. |
| Official study material from CompTIA | Official study material for CompTIA certs from CompTIA (e.g., CertMaster) is pretty lackluster. | ||
| Udemy Courses | Can be extremely cost-effective (never buy anything at full price! Always wait for a sale!) Public reviews + course sale counts indicate whether people liked the courses, letting you know if courses are worth your time | Udemy courses have a fairly limited format (videos, quizzes, some written material). Very few Udemy courses have lab components. Udemy courses are not “certifications” and you generally should not brag about completing them. | I regularly work through Udemy courses for fun/personal growth. For CompTIA certifications, I recommend Udemy courses any day of the week as one of my favorite learning sources. |
| Security Blue Team | Hands-on labs High-quality written content Better cost/benefit ratio than many other platforms BTL1 is a decently well-regarded junior SOC analyst certification | Their cloud labs, though decent-quality, take a long time to spin-up and are unfortunately pretty laggy. | |
| Microsoft Learn | Microsoft Learn is extremely comprehensive and usually well-written. Microsoft Learn is free! | Microsoft documentation is often complex. This is generally because their products are overly complex. | |
| Cisco | Cisco-published books (e.g., those by Wendell Odom) are plain good. | Cisco online training is unreasonably expensive, particularly if trying to accumulate credits for certifications. | Cisco training ranges between “okay” and “good.” They are often the only place to learn their proprietary tooling. |
| Linux Professional Institute | LPI is a high-quality and free resource for learning a lot of beginner Linux content. | I highly recommend going through LPI’s Linux Essentials and LPIC-1 content for learning Linux if you’re new to it. | |
| Applied Network Defense | On-demand, self-paced, high-quality courses with great labs taught by experienced cybersecurity analysts. | Courses are slightly expensive. | |
| TryHackMe | Good, relatively cheap, and fun! Has a decent amount of both blue team and red team content. | The “ceiling” (difficulty, challenge, complexity) of TryHackMe is generally lower than HackTheBox | I’d generally recommend TryHackMe for “anyone” or to “get your feet wet” |
| HackTheBox | Very high quality, offensive security-focused training, largely in a CTF format. | HackTheBox has monetized very heavily in recent years; it’s hard to play without paying. | I’d recommend HackTheBox to anyone who wants to focus on offensive security learning and has exhausted the best content of TryHackMe |
| Books | There are a lot of awesome books out there! The medium of a book lends itself well to lengthy, deep topics | Reading books can be slow Books can fall out-of-date quickly | I highly recommend the books from No Starch Press. I rarely buy a book if I am not able to acquire a PDF/eBook version of the book (due to lack of CTRL + F searching) |
For my thoughts on college, check out the appendix entry at the end of this post.
How do I Learn?
There are a million different learning styles. The only true answer to “How do I learn?” is “Whatever works for you!” That said, I do have opinions on some best practices I think anyone would do well to consider.
Take Notes
If you’re going to learn something, you should write it down somewhere. I strongly believe in digital note-taking since it allows you to easily rediscover old notes, keep screenshots, store long text snippets, and quickly find items of interest via CTRL + F. I am currently using Obsidian and have previously used Microsoft OneNote and Microsoft Word. Some pros and cons I’ve experienced with different note-taking platforms are as follows:
| Platform | Pros | Cons | Comments |
|---|---|---|---|
| Obsidian | - Supports markdown - Is extremely extensible - Completely free - Everything is a file. All notes are separate files under a single folder you specify as an Obsidian “vault.” If you sync your vault with OneDrive, Google Drive, etc., you have access to your Obsidian notes everywhere | - All sorting is alphabetic by default, meaning - Extensions required for some “basic” functionality - Mobile usage can be clunky (I use Google Drive + the “DriveSync” app on Android) - Searching becomes slow over time - Poor performance for “monolithic” notes (e.g., 300 pages in one doc) - Given the nature of having bazillions of smaller notes linked together, it is difficult to export content to other platforms - There is a learning curve depending on how “deep” you want to go with Obsidian. | There is a contingent of Obsidian users who have dedicated their lives to creating a utopian personal knowledge management system. Feel free to only go as far as you want and don’t be intimidated by others. |
| OneNote | - Free - Syncing in accordance with Microsoft account / OneDrive - Indexes on text in screenshots, so you can search (CTRL +F) for text in pictures | - Once OneNote has a sufficiently large amount of notes, searching becomes unreliable (not even finding notes based on content in title of a note) - I’ve personally experienced OneNote syncing undo hours and hours of work multiple times | OneNote is probably the application with the broadest ease of use and usability. This is my first recommendation to most folks. |
| Microsoft Word | - Word Docs are some of the easiest to export to other formats - Good for monolithic notes | - Hard to search for content if you’re outside the note document for a particular subject. Protip: in Microsoft File Explorer, use “content:<text>” to search for indexed text of interest in files like Word docs. - Lack of organization features | I spent most of my years of note-taking in Microsoft Word due to its simplicity. |
| Physical Notes | - None | - Takes up physical space - Hurts your hands after writing - 1000x less rediscoverability of information - Subject to water damage, fires, polar bear attacks | I have never been able to find any note I wanted to find from a physical notebook more than one month after the notebook stopped being immediately relevant to me. |
Culminate Your Learnings with a Project
I believe the end of any chapter of your learning journey should culminate in some kind of a project. A “project” doesn’t need to be something elaborate. For example, you don’t need to go write the successor to Volatility after spending a couple of months learning Python. A project just needs to be something moderately “chunky” that incorporates the expanse of the knowledge you’ve accumulated. Examples of “projects” I’ve completed include dissecting a “complicated” (relative term) piece of malware, completing a forensic investigation on an intricate disk/memory image, passing a certification exam, and giving a presentation to my local security community. Giving presentations also doubles as a great way to meet people and introduce yourself to the security community!
Getting Off Tutorial Island
After you’ve spent some time — maybe a couple of years — learning and developing core skills, you might find that things begin to feel “samey” and that you are revisiting the same concepts over and over. This plateau is common, and it is generally an indicator that you’re ready to move beyond beginner material.
I was recently reminded of this by a post from Graham Helton (a wonderful brain in cybersecurity) that commented on “Tutorial Island.” In a video game, “Tutorial Island” is the starter area where you learn how to play the game before moving on to the rest of your adventure. Below is a screenshot of the literal Tutorial Island in RuneScape.

In Cybersecurity, Tutorial Island, as I interpret it, is the overabundance of early/beginner-level content in the form of tutorials, entry-level certifications, free courses, flash card compilations, YouTube playlists, and so on. Tutorial Island is a great place to start out, but, at some point, you’re going to want to move on and continue your journey.
As an example, let’s say, in the realm of certification, you’ve achieved the CompTIA entry-level trifecta: A+, Network+, and Security+. Should you now pursue CCT (Cisco Certified Technician) as the next “step up” in your networking game? No! You should have a great foundation in place for an early career role in IT. You don’t need to keep revisiting the same basic concepts over and over - you are ready to try to tackle more complex things. If you’re going to pursue another certification, it should at least be a large step up in complexity (e.g., CCNA) or a new topic (e.g., Linux administration). But also think outside of certifications. For example, a great project you could do that will pay dividends later would be to build a home lab network. You could get fancy with things like NAT, VLANs, and firewall rules — and even learn how to manage a hypervisor (e.g., Proxmox).
Some things also simply cannot be found on Tutorial Island. For example, not one of all of the Udemy courses in the world can engrain in you the experience of building and maintaining an open-source project from scratch. Oftentimes, the only way to grow is by doing.
The Soft Stuff
The vast majority of this blog post has covered the what, when, where, why, and how of hard (technical) skills. Equally important, however, are soft (people) skills. In the modern age, if you can’t work well with others, there are very few workplaces where you can thrive. I’m not a master of social wizardry, but I fare well enough following some key pieces of advice.
Social Best Practices
“Criticisms are like homing pigeons. They always return home.” - Dale Carnegie - Criticizing peers, especially in a public setting, very often backfires and can be held against you for a long time. In situations where you have to highlight the shortcomings of a peer (e.g., coaching a junior colleague), I recommend being extremely attentive, calm, patient, understanding, and kind. Never be dismissive.
The best way to build a relationship is to care for and help people in a time of need - Helping folks when they’re struggling is just a plain good thing to do, and you will often find your efforts deeply appreciated.
The best way to build your reputation is to let other people do it for you - No one trusts a self-endorsement. When we are told someone (or something) else is great by someone we trust, however, we are significantly more likely to believe it. Thus, the best way to build your reputation is to cause people to like you and let those people “spread the word.”
Influence grows through broad weak ties, not tight-knit cliques - You will be able to get a lot more done if you have relationships outside of your immediate team. Consider the following example:
Example 1: Bob
Bob is an Incident Response Analyst. He wants to stand up the Malware Information Sharing Platform (MISP) to help build out the threat intel program. He has no relationships outside of his team. He submits a ticket to the engineering team’s work intake queue. It takes 4 months for resources to be allocated. The security review is then delayed weeks by a lack of a response from a vendor on what TLS version they intend to support in 6 months. Once the server is finally provisioned, it turns out that additional firewall rules are needed to sync data from one of the intel feeds. Bob submits another ticket which bounces between teams for weeks. By the time everything is working, six months have passed, and the threat intel analyst who was hired to help maintain MISP has rebounded to his previous employer after not having any meaningful work to do. Bob laments the situation with his peers who all agree that the situation sucks.
Example 2: Alice
Alice is an Incident Response Analyst. She wants to stand up MISP to help build out the threat intel program. She spends the first hour of everyday walking through the sea of cubicles at the office, chatting up folks outside her team. She asks Jason, a server engineer, about the possibility of getting a MISP server spun up. Jason, who loves the Hi-Chew candy Alice brings her every Tuesday spins up the server that night in the lab environment and promotes it to prod in the morning after making sure his boss is fine with that. The next day, while at lunch with Taylor from the network engineering team, she laments the fact that the MISP server isn’t able to sync data from one of its most important feeds. Taylor, who brought her laptop to lunch, checks the firewall logs, identifies the undesirably blocked network connection, and writes a new firewall rule to allow the connection. It has taken about two days, but the MISP server is finally up and running. Alice is then promoted to Senior Incident Response Analyst and awarded the Presidential Medal of Freedom.
TL;DR:
Having lots of disparate relationships allows you to get things done faster and better, share and gather useful information, and connect others to multiply impact.
Improving Social Skills
I was not born excellent at socializing. In fact, I might still be bad at it. But I am a lot better than I used to be. I’ve got good and bad news.
The good news is that you can improve your social skills. Words cannot express how profoundly socially inept I used to be. I am no longer that person. Improvement is possible.
The bad news is that you are going to have to socialize. There’s no way around it. Socializing skills are like a muscle. They need to undergo exercise to grow. Sometimes, that exercise is very painful.
Things I’ve found beneficial to my social skills include:
- Introducing yourself to people one at a time: it’s often hard to get to know someone or build a relationship in a group setting. Chatting with people one-on-one builds relationships faster.
- Learn to take a deep interest in others. Most people’s favorite topic is themselves. If you can learn to be engaged with other people and what they are interested in, you can go far.
- Offer friendly greetings when encountering people. A simple smile, “hello,” or “cool shoes” goes a long way.
Prioritizing
Some people are outwardly doing “all the right things,” yet failing to succeed. Commonly, this is because they are simply doing things in the wrong order, resulting in important work never getting done. One helpful tool for managing priorities is the Eisenhower Matrix. Below is its conventional depiction.
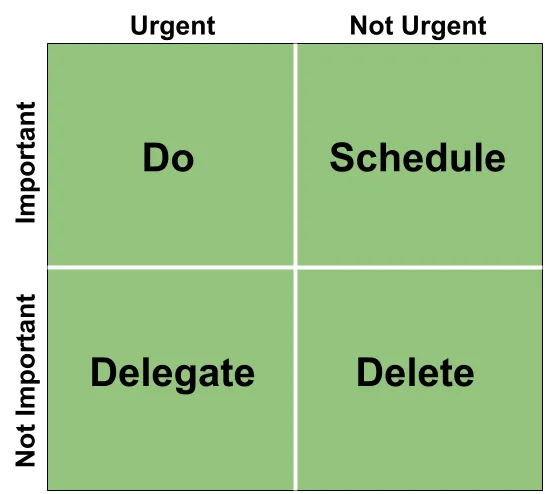
The basic idea is simple:
- Do tasks that are important and urgent
- Schedule tasks that are important but not urgent
- Delegate tasks that are urgent but not important
- Eliminate tasks that are neither important nor urgent
This is not bad advice. However, it is not what I do. The “Isaac version” of the Eisenhower Matrix is below.
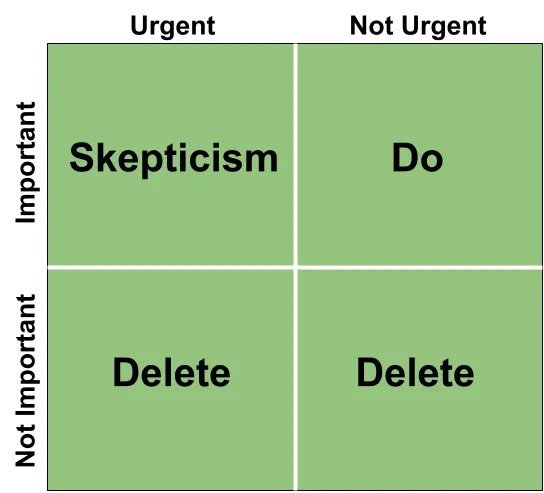
My biggest change is shifting from focusing on urgent, important tasks to non-urgent, important tasks. Why do this? Because most things that we are told are urgent and important are simply… not. I’m regularly met with tasks that are “the most important thing ever” that “need to get done immediately.” Very, very, very rarely do they ever happen to be so. I prefer to push the envelope on waiting on such tasks to see if they really matter.
Other times, important, urgent tasks do end up being exactly that. Consider homework that is due the next day. Clearly that is important, and it needs to be done by tomorrow, so you should work on it ASAP, right?
I still advocate for focusing on non-urgent important tasks before such things. Why? Consider the following example:
Situation: Billy
Billy’s college homework is due at 8:00 AM tomorrow. Billy gets home from his college classes for the day at 3:00 PM. He wants to be a SOC analyst, so he’s taking the Blue Team Level 1 certification course. He has three months left to take the exam and won’t be on the job market for at least another year, so neither the training nor the certification is urgent.
Branch A: Focusing on the Important + Urgent
Billy decides to prioritize his important and urgent homework. He spends three hours plugging away at the homework, finishing at 6:00 PM. He probably could’ve finished the homework sooner, but he had the entire evening to get it done, so he took a few breaks and was distracted while he worked. Once he finished his homework, he felt it was getting late and he might as well relax for the rest of the evening.
Result: Billy has completed his homework
Branch B: Focusing on the Important + Non-Urgent
Billy decides to spend two hours progressing through the BTL1 course. At 5:00 PM, he remembers he needs to get his homework done and pivots to that work. He wraps two and a half hours later at 7:30 PM. Tuckered out, he prepares for bed after a very productive day.
Result: Billy has completed his homework and made meaningful progress on a long-term goal.
In a nutshell, you can “put off” urgent, important work until after you do some non-urgent work to squeeze more productivity out of yourself.
This works very well for me, as I am someone who refuses to not get important things done, even if it causes me to work later into the evening than my weak willpower would typically prefer. I would not recommend this strategy if you are someone who presently struggles to complete important tasks.
Conclusion
Everyone’s path into this industry looks a little different. Some people get a computer science degree. Some people start in a help desk role. Others start by tearing malware apart on nights and weekends. There’s no single “right” way to do it all — but there are definitely better strategies for navigating the early-career maze. My hope is that this post will help folks find a path in their IT & Cybersecurity journey that is both productive and painless.
Here’s what I hope sticks with you:
- Know what you want to do (even if it’s only a rough idea)
- Learn skills that are not just interesting, but relevant
- Choose learning materials that respect your time (#1) and your budget
- Take notes
- Don’t underestimate people skills
- Always keep marching forward.
Appendix
College
Do you NEED to go to college for IT or cybersecurity? Nope! SHOULD you go to college for IT or cybersecurity? Maybe!
I have a bachelor’s degree in Information Assurance & Cyber Defense (renamed to “Cybersecurity” a year after I graduated) from Eastern Michigan University. I’m overall happy that I went, though I don’t think my time or money was always well spent. I think the question of “Should I go to college?” can only be answered by analyzing the costs and benefits you would experience.
Considerations that might make me more likely to consider attending a college include:
- The publicly-listed instructors have proven experience outside of academia in IT or cybersecurity
- The curricula are regularly updated
- The cost of tuition is not ridiculous
- The institution is accredited
- The institution has an active student-led cyber organization
My favorite parts about my college experience were a robust cyber student organization, awesome courses with real-world value authored by the great Chris Krieger, and excellent instruction on digital forensics from other experienced professionals. My main complaints: high cost, the fact that most of the instructors were either grad students or PhDs in unrelated fields, and that many of the courses were outdated or copied-and-pasted from some course catalog for beginner industry certifications.
Honorable Mentions
The following colleges/universities deserve a mention:
The SANS Technology Institute - SANS provides the highest quality cybersecurity training, period. The SANS.edu courses are variations on their normal courses, and you earn certifications along the way. Many noteworthy folks have come out of its MSISE (Master of Science in Information Security Engineering) program. The only downside is that its cost is very high. It may be best to attend the SANS.edu leveraging either veteran or corporate benefits.
Western Governors University - WGU is popular as an accredited, low-cost, remote, flexible option to get a degree in IT or security. Many of their courses are based on industry certifications, allowing you to become certified as you progress through college. Additionally, their courses are self-paced, meaning you can complete some courses very quickly and graduate “early.” The downsides to WGU are that it is perceived by some as a “cert mill” (a low-quality institution that exists to pump out students with certifications), that its instruction is often very “hands-off” (teach yourself), and that it requires significant self-discipline to get through the program, as it is pretty much entirely self-guided.
State Schools - Public colleges and universities in your state (like the one I attended) are generally fine. They’re typically a mixed bag of gold bars and snapping turtles. Their IT/cyber programs, if successful, are likely reliant upon a few key instructors holding up the program. They probably have some truly remarkable classes alongside some truly despicable, abject failures of classes. They might have good cyber student organizations, or their cyber student organizations might have died some years ago after “drama” happened. Most range in quality between 5/10 and 7/10, fluctuating slightly from year to year.
Computer Science vs Cybersecurity vs IT Degrees
For a career in IT, I think you should pursue a degree in IT. Neither a degree in computer science nor cybersecurity will hurt your prospects for a career in IT, but I think an IT degree gets you off the ground faster.
Computer science and IT differ in abstraction levels, much like math and engineering. Math is pure and logical, while engineering simplifies it for real-world use — turning precise equations into approximations like v = -10t + u for gravity. Similarly, computer science deals with pure, logical, low-level concepts like CPU registers and memory pointers, whereas IT abstracts these away, focusing on practical tasks like troubleshooting, patch management, and network security.
xkcd 435 is relevant here.
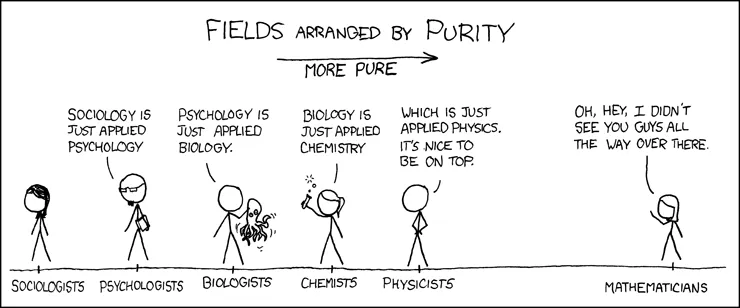
Most cybersecurity degrees are functionally somewhere between a computer science degree and an IT degree. Some concepts, like digital forensics, exist in their own, distinct realm that don’t easily fall into IT or computer science skills, and those will stand out as unique in a cybersecurity degree. The rest, however, is somewhere along that spectrum.
I believe that a computer science degree, or a computer science-focused cybersecurity degree, is better in the following situations:
- You want to work in offensive security (e.g., red teaming, penetration testing)
- You want to do advanced security research (e.g., reverse engineering malware, creating new products and tools to fight malware)
- You want to ensure that code is secure (application security)
- You want to thrive later in your career (most advanced cybersecurity roles necessitate some proficiency in coding/scripting)
I think that a cybersecurity degree, or an IT-focused cybersecurity degree, is better in the following situations:
- You want to work in digital forensics and/or incident response (investigating and responding to cyber intrusions)
- You want to work in a general SOC role (continuous detection + monitoring of networks for signs of intrusion)
- You want access to the cushion of being able to pivot to any job in IT if the cybersecurity industry declines
- You want to thrive early in your career (there are more IT + blue team jobs available at entry level than red team / advanced security research roles)
Red vs. Blue
“Red vs. Blue” is not just a cult-classic Halo machinima from 2003. It’s also a debate that many fresh faces at the entry level contend with. When I say red team, I’m using it as shorthand for offensive security roles (e.g., penetration testing, exploit development, adversary emulation), whereas blue team refers to defensive security roles (e.g., SOC analyst, incident response, GRC).
As a disclaimer, I’m very thoroughly blue. Outside of doing some malware development courses from Sektor 7 (to help understand Windows internals + low-level coding), completing some pathways on TryHackMe, and achieving the PenTest+ certification, my blood runs blue. I’ve only worked in IT & defensive roles. All of my cybersecurity friends work in defensive roles. Nearly all my coworkers are involved in inherently defensive roles.
Some folks assert that there are plenty of open roles for red team work, but I don’t see them. I’ve heard there may be more opportunities for such roles in the government, but I am unfamiliar with that.
My blue boots-on-the-ground view of working in a “red team” role is that there are some challenges to the prospect. The following are some of my biggest concerns with the notion:
- I’ve observed organizations lose dedicated offensive security talent over time, as it is both expensive and difficult to maintain that capability in-house.
- Jobs like bug bounty have been hit hard by race-to-the-bottom economics driven by global competition. I know people significantly smarter than me who are not able to make a living wage discovering vulnerabilities in software.
- If an organization has to cut its security budget, it’s probably more likely to keep roles dedicated to defensive measures as opposed to the roles that enhance defensive capabilities through offensive means (remember, many organizations are barely willing to do more than pay for an annual external “pentest”).
If you DO want to work on the offensive side of the house, I can only recommend getting very good at your craft and marketing yourself very well; you’ll need to do more to stand out for a small, picky audience amongst a large crowd.
Private vs. Public
A common question folks early in their IT/cybersecurity careers have is whether they should work in the private sector (companies) or in the public sector (the government). I’ve spent my whole life in the private sector, so I can’t speak from firsthand experience about government work, but I’ve run into many people who have worked on both sides of the fence.
Common positive things I hear about working in the public sector include:
- The benefits and holidays are great
- Veteran benefits are super great
- You can acquire security clearances (generally at military/national security-adjacent roles) which open up many lucrative opportunities in the private sector once you leave public sector work
- The mission of many government agencies is held in very high regard and some of the most awesome and admirable people on the planet work for the government
- There’s usually great job security (unless the year is 2025)
Common negative things I hear about working in the public sector include:
- Working digital forensics for law enforcement (particularly at the entry-level) may necessitate hours of viewing profoundly obscene imagery. I know people who left cybersecurity because this was their first exposure to the field.
- The pay pretty much always stinks
- It’s hard to attract and retain talent in government jobs. It is also hard to remove unwanted talent (crappy coworkers may never get fired).
- You have the worst bosses ever: congress and/or the president
- Working in the military can be very rewarding and interesting, or it can end up with you being assigned doing something you have no interest in while living in housing that is actively killing you.
In short, I think that if you’re going to do public sector work, you should probably do it early in your career to enhance your private sector opportunities later. Many of the best cybersecurity institutions in the world today were born out of the best and brightest of our military veterans. Alternatively, you may join the public sector late in your career when you’re more interested in stability and benefits for your family.